Professional Services
We provide professional cybersecurity services designed to protect your business from evolving threats and vulnerabilities.
Our expert team delivers end-to-end solutions including risk assessment, monitoring, and incident response tailored to your environment.
With a proactive and compliance-driven approach, we ensure your web Apps, systems, networks, and data remain secure and resilient.

PENETRATION TESTING & RED TEAMING
Before real adversaries find your weaknesses, we do. Our certified penetration testers and red teams conduct simulated attacks across your networks, applications, and physical environments to uncover exploitable vulnerabilities. From targeted pen tests to full-scale red team operations, we deliver detailed findings and actionable remediation guidance and turning discovered weaknesses into strengthened defenses.
Key Capabilities:
✔ Network, web application penetration testing
✔ Red team adversary simulation exercises
✔ Social engineering and phishing assessments
✔ Detailed reporting with prioritized remediation roadmap

Think Like an Attacker. Defend Like a Pro.

RISK MANAGEMENT & COMPLIANCE
Navigating today's regulatory landscape requires more than checkbox compliance. It demands a proactive risk culture. Our team delivers comprehensive risk assessments, threat modeling, and regulatory compliance advisory across frameworks such as ISO 27001, NIST, NCA ECC, and GDPR. We help you identify vulnerabilities before they become liabilities and implement practical controls that satisfy auditors and protect your business.
Key Capabilities:
✔ Enterprise risk assessments & threat modeling
✔ Regulatory compliance advisory (NCA ECC, ISO 27001, NIST, GDPR)
✔ Risk register development and continuous monitoring
✔ Third-party and supply chain risk management

Stay Ahead of Risk. Stay Compliant.

CYBERSECURITY ARCHITECTURE
We design robust, scalable security frameworks tailored to your organization's unique infrastructure. Our experts develop comprehensive security policies, governance processes, and technical blueprints that align with industry’s best practices and ensuring your systems are secure by design, not by chance. From zero-trust models to layered defense strategies, we architect protection that grows with your business.
Key Capabilities:
✔ Custom security framework design & documentation
✔ Zero-trust and defense-in-depth architecture
✔ Security policy and governance development
✔ Architecture review and gap analysis

Build Security from the Ground Up

CLOUD SECURITY
As organizations accelerate their cloud adoption, security must keep pace. We secure your cloud infrastructure whether AWS, Azure, Google Cloud, or hybrid environments through robust encryption, identity and access management, continuous monitoring, and compliance automation. Our cloud security specialists ensure your data and workloads remain protected at every layer, from storage to compute.
Key Capabilities:




Secure Every Layer of Your Cloud.

IDENTITY & ACCESS MANAGEMENT (IAM)
Controlling who can access what and when is one of the most critical pillars of cybersecurity. Our IAM services establish a centralized, policy-driven framework that manages digital identities across your entire organization. We implement authentication, authorization, and single sign-on (SSO) solutions that reduce the attack surface, enforce least-privilege principles, and deliver seamless access experiences for employees, partners, and customers alike.
Key Capabilities:
✔ Identity governance and administration
✔ Single Sign-On (SSO) and Multi-Factor Authentication (MFA) implementation
✔ Role-based and attribute-based access control (RBAC / ABAC)
✔ Identity lifecycle management and automated provisioning/de-provisioning

Right Access. Right People. Right Time

PRIVILEGED ACCESS MANAGEMENT (PAM)
Privileged accounts are those with elevated access to critical systems, databases, and infrastructure are among the most targeted assets in any cyberattack. Our PAM services provide strict oversight and control over these high-value credentials, ensuring that privileged access is granted only when needed, fully audited, and automatically revoked. We help organizations prevent insider threats, contain breaches, and maintain full visibility over their most sensitive access pathways.
Key Capabilities:
✔ Privileged account discovery, vaulting, and rotation
✔ Just-in-time (JIT) access and session isolation controls
✔ Full privileged session recording and audit trails
✔ Privileged threat analytics and anomaly detection

Secure the Keys to Your Organization.

DATA LOSS PREVENTION (DLP)
Data is your most valuable asset and one of your greatest liabilities if left unprotected. Our DLP services identify, classify, and monitor sensitive data across your endpoints, networks, and cloud environments to prevent unauthorized access, sharing, or exfiltration. Whether protecting personal data, intellectual property, or financial records, we implement intelligent DLP policies that enforce compliance, reduce data breach risk, and maintain trust with your customers and regulators.
Key Capabilities:
✔ Sensitive data discovery, classification, and labeling
✔ Endpoint, network, and cloud DLP policy enforcement
✔ Regulatory compliance support (SAMA, NCA ECC, PCI-DSS, HIPAA)
✔ Real-time alerts, incident response, and DLP reporting

Keep Sensitive Data Where It Belongs
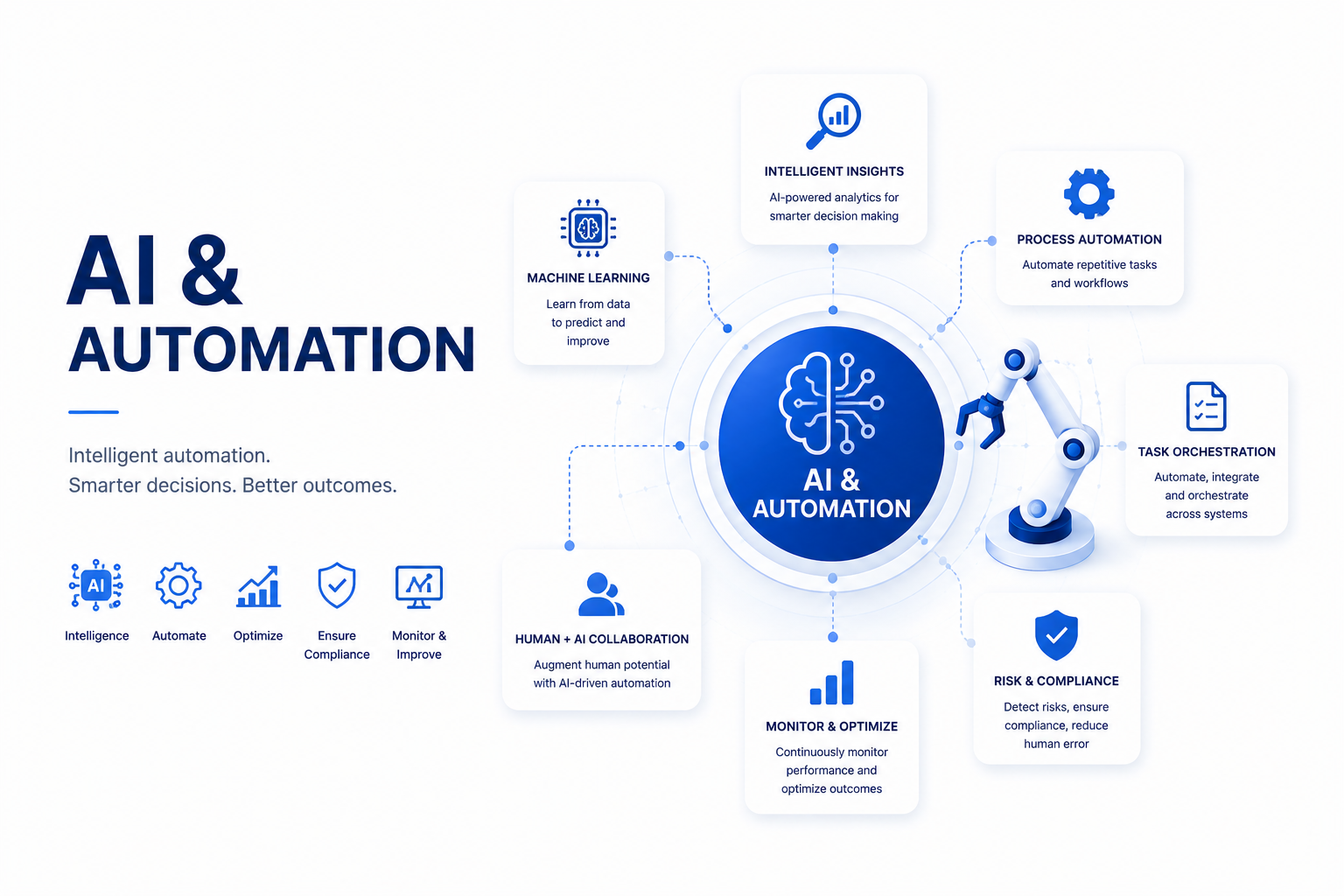
AI & AUTOMATION
Harness the power of artificial intelligence and intelligent automation to transform your business operations. We design and implement data-driven decision-making tools, workflow automation solutions, and AI-powered analytics platforms that eliminate manual bottlenecks, reduce operational costs, and provide real-time insights. From predictive analytics to robotic process automation (RPA), we help you unlock the full potential of your data.
Key Capabilities:
✔ AI-powered analytics and business intelligence dashboards
✔ Process automation and robotic process automation (RPA)
✔ Predictive modeling and data-driven decision tools
✔ Custom AI solution development and integration
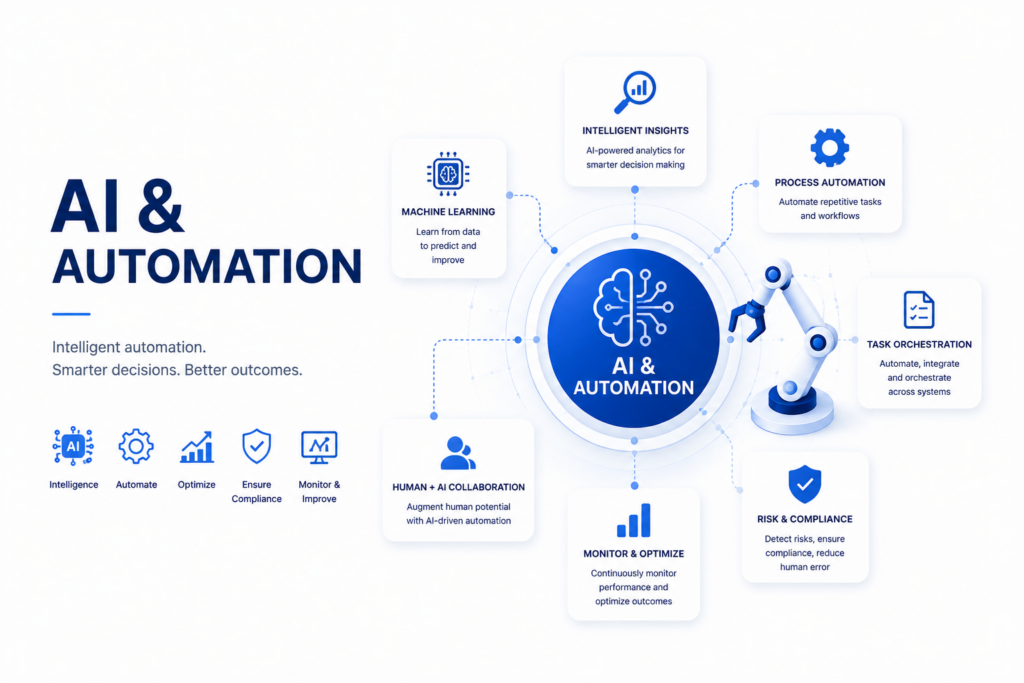
Smarter Decisions. Faster Processes.
ISO 27001
We help organizations achieve ISO 27001 readiness through structured gap assessment, risk management, and full implementation of compliant security controls.
NCA
We support organizations in achieving National Cybersecurity Authority compliance by aligning their policies, controls, and processes with national cybersecurity frameworks and requirements.
SAMA
We help financial institutions achieve compliance with Saudi Central Bank by aligning their cybersecurity controls with SAMA’s Cyber Security Framework, ensuring robust risk management, data protection, and regulatory adherence.


